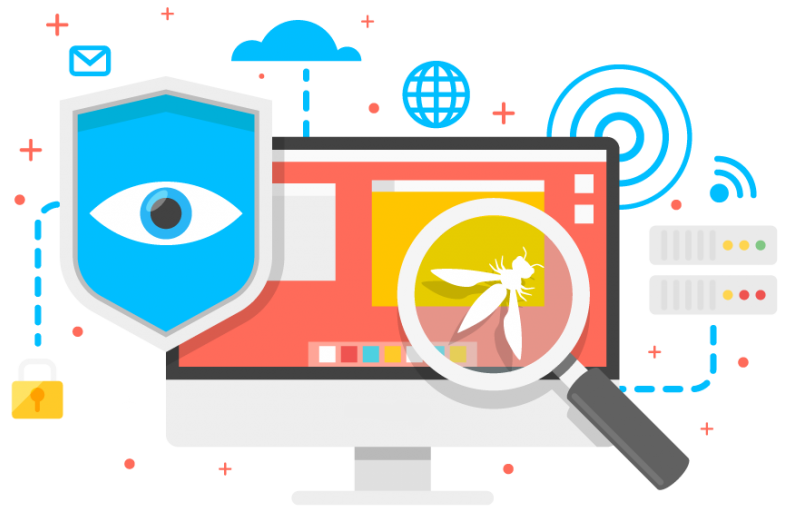
Are you Secure?
There is a hacking attempt every 39 seconds (University of Maryland). Our experts can help you remove existing infections while preventing new ones.
Are you Up-to-Date?
A system with vulnerabilities is an insecure system.
Our maestros will keep your systems patched with the latest updates preventing attacks before they even occur.
Are you next?
43% of cyber attacks target small business.
Let our professionals help you protect that, which matters most.